Understanding the Role of ICMP in Network Diagnostics and Messaging
Post Preview
Key Takeaways:
- Insight into the indispensable role of the ICMP protocol in network troubleshooting and messaging.
- Detailed exploration of different ICMP message types and their applications in networking.
- Discuss how ICMP is leveraged within network security to safeguard systems while maintaining communication integrity.
- Introduction to various ICMP-based tools and resources that aid networking professionals in diagnostics.
Table of Contents:
- What Is ICMP and How Does It Work?
- The Types of ICMP Messages and Their Uses
- ICMP and Its Impact on Network Security
- Implementing ICMP in Network Troubleshooting
- Comparing ICMP with Other Diagnostic Protocols
- How ICMP Interacts with Other Network Protocols
- ICMP Tools and Resources for Networking Professionals
What Is ICMP and How Does It Work?
Internet Control Message Protocol (ICMP) is an essential part of the Internet Protocol Suite for sending error messages and operational queries and providing feedback about network communication issues. It serves as the network’s messenger by alerting devices to their communication status and issues. This is analogous to a body’s nerve system relaying pain, which prompts a response to potential hazards. ICMP performs its duties without carrying application data but instead manages the messages about the data’s flow between network devices.
For example, when a user attempts to reach a down web server, ICMP communicates back to the source about the problem with a “destination unreachable” message. From limited to error notification, ICMP is also utilized for network troubleshooting and maintenance tasks, ensuring that networks run efficiently with minimal interruptions. This crucial behind-the-scenes action is a foundational element that keeps digital information flowing smoothly across diverse and complex network topologies.
The Types of ICMP Messages and Their Uses
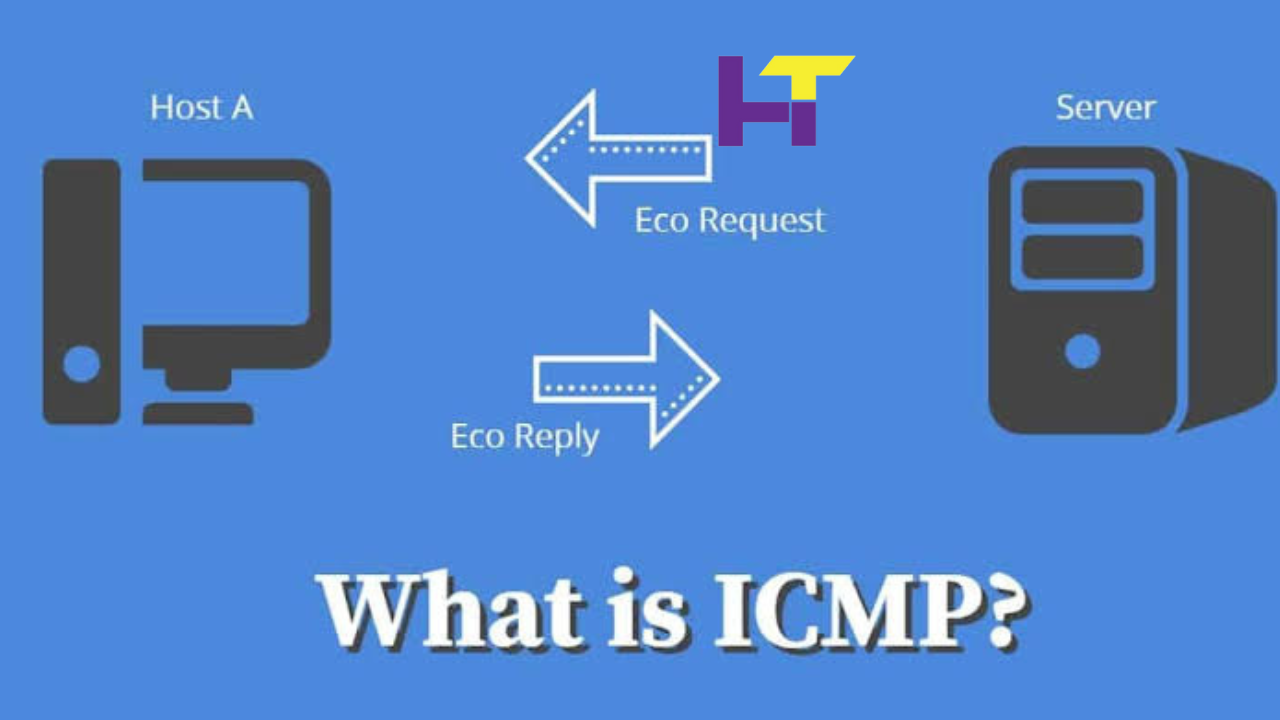
ICMP messages come in various forms, each corresponding to different network contexts and issues. The error-reporting messages include destination unreachable, source quench, redirect, time exceeded, and parameter problem, each carrying distinct information about the network’s state. On the other hand, query messages, like echo requests and replies (used in ping operations) and timestamp requests and replies, help ascertain the operational status and connectivity between network points. The versatile combinations of these messages allow network administrators to diagnose and resolve issues efficiently.
ICMP’s “echo request” and “echo reply” messages are the backbone of the ubiquitous “ping” tool. This function helps isolate whether connectivity issues are present—a foundational step in any network troubleshooting procedure. The speed and simplicity of a ping command exemplify ICMP’s direct approach to network diagnostics and act as a first-line tool for checking Internet connections. Optimizing these messages can greatly influence network performance to provide prompt and accurate feedback about connectivity.
ICMP and Its Impact on Network Security
While ICMP offers significant benefits in diagnostics and network messaging, it has challenges, particularly regarding security. Attackers can exploit ICMP to perform malicious activities, such as using the protocol for network scanning or conducting Denial of Service attacks by flooding a target with ICMP packets. Therefore, network administrators employ ICMP carefully, finding a balance between usability and security.
Deploying strategic ICMP filtering and rate limiting are crucial tactics used to enhance network security without losing the advantages of the ICMP protocol. For example, a firewall might be set up to allow ICMP echo replies but not timestamps or address mask requests, minimizing the risk of network surveillance. Moreover, careful examination of the ICMP traffic can reveal unusual patterns that might indicate security threats, enabling proactive responses to potential intrusions. Understanding the dual nature of ICMP—both a tool and a possible attack vector—is essential for robust network security.
Implementing ICMP in Network Troubleshooting
Effective network troubleshooting relies on a thorough understanding of the tools at one’s disposal, among which ICMP is particularly prominent. When identifying the source of network anomalies, ICMP furnishes immediate and clear signals about the presence and nature of connectivity issues. For instance, networking professionals can pinpoint where packet loss or latency spikes are occurring using the “traceroute” command, which employs ICMP messages to map the journey of packets from one node to another.
This protocol proves its worth in responding to existing problems and preemptive monitoring, potentially alerting to impending issues before they fully manifest. Utilizing ICMP in preventive and reactive manners provides a well-rounded approach to sustaining network health. This preventive capability is vital for ensuring the uptime of critical services and maintaining a high network performance level.
Comparing ICMP with Other Diagnostic Protocols
ICMP functions alongside a suite of protocols, each with specialized roles within a network. While ICMP excels at quick diagnostics through its messaging capabilities, other protocols offer different features. For example, the Simple Network Management Protocol (SNMP) provides a framework for collecting and organizing information about network devices, offering a more granular control over network performance and configuration than ICMP’s messaging system.
Each protocol serves its purpose and offers unique network diagnostics and management advantages. The specific requirements of the situation determine the choice of when to use ICMP over other protocols, like SNMP or TCP/IP. Successful network management demands familiarity with these tools and the wisdom to apply them appropriately.
How ICMP Interacts with Other Network Protocols
In the intricate dance of network protocols, ICMP plays a pivotal role in maintaining the rhythm of communication. It operates with others, primarily the Transmission Control Protocol/Internet Protocol (TCP/IP) suite, to ensure adequate data flow across the network. While TCP/IP handles the actual transit of data, ICMP works behind the scenes, monitoring and managing network conditions to enhance communication. This symbiotic interaction between ICMP and other protocols is integral to keeping network infrastructure resilient and adaptive to dynamic operational demands.
ICMP Tools and Resources for Networking Professionals
The toolkit of a networking professional is replete with ICMP-embedded tools that cater to diagnostics and network health monitoring. The most immediate and familiar of these tools are the ping and traceroute utilities, built into most operating systems. In addition, ICMP also lends itself to more advanced network analysis and monitoring suites that offer a broader range of diagnostic abilities. To stay effective in an ever-evolving technological landscape, networking professionals must constantly expand their toolkits and stay abreast of innovations in ICMP tools and techniques.
Read More: Emerging Cybersecurity Threats: Stay Ahead of Hackers.






